One of the most significant advantages of Java is its memory management. You simply create objects and Java Garbage Collector takes care of allocating and freeing memory. However, the situation is not as simple as that, because memory leaks frequently occur in Java applications.
This tutorial illustrates what is memory leak, why it happens, and how to prevent them.
1. What is Memory Leak?
Definition of Memory Leak: objects are no longer being used by the application, but Garbage Collector can not remove them because they are being referenced.
To understand this definition, we need to understand objects status in memory. The following diagram illustrates what is unused and what is unreferenced.
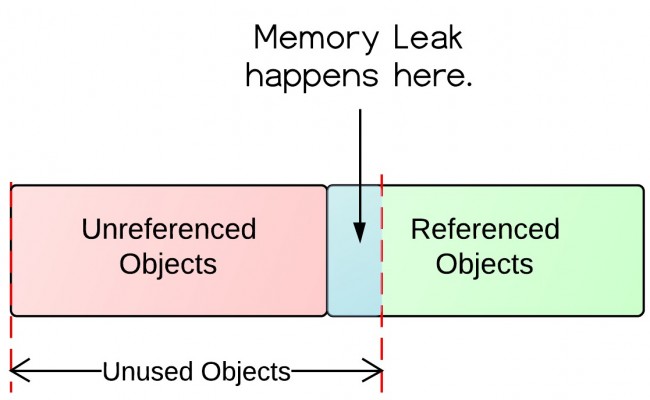
From the diagram, there are referenced objects and unreferenced objects. Unreferenced objects will be garbage collected, while referenced objects will not be garbage collected. Unreferenced objects are surely unused, because no other objects refer to it. However, unused objects are not all unreferenced. Some of them are being referenced! That’s where the memory leaks come from.
2. Why Memory Leaks Happen?
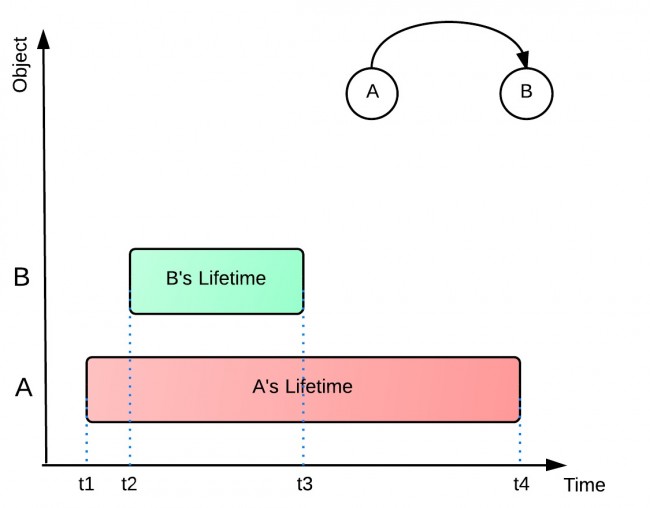
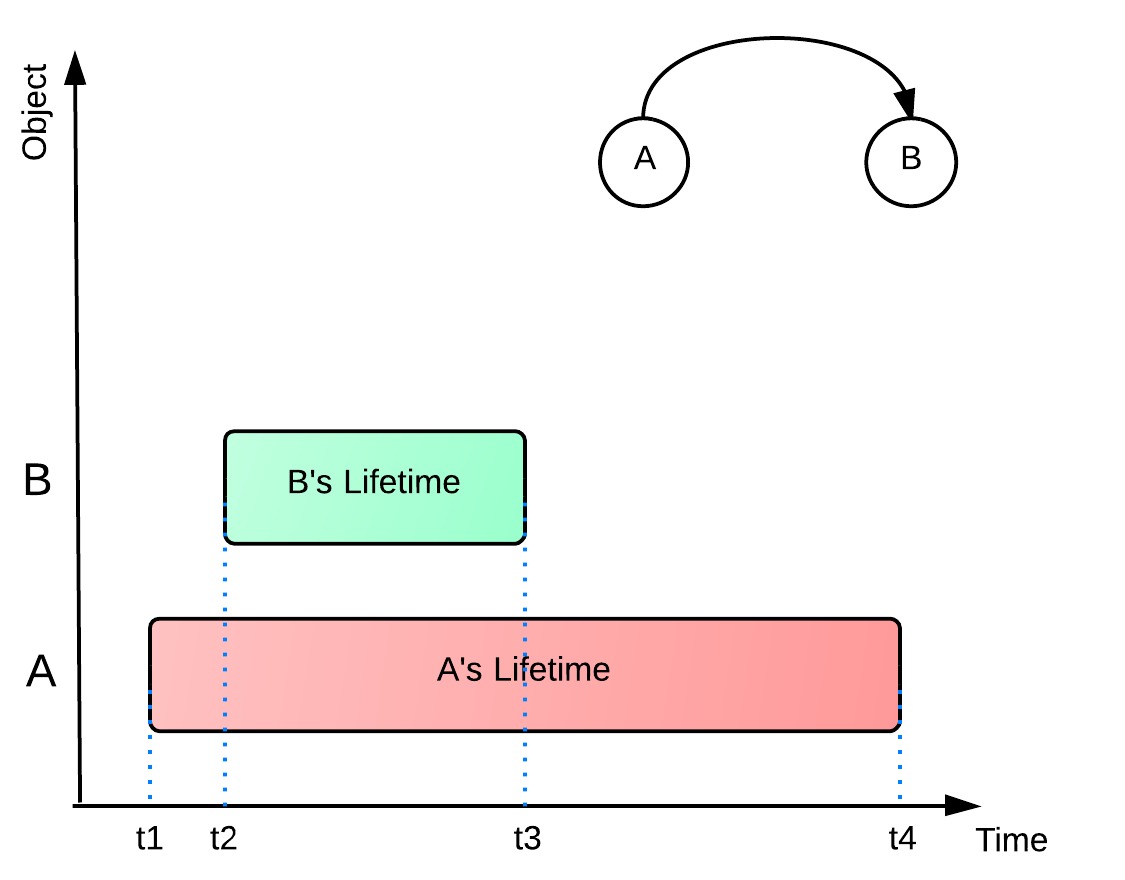
Let’s take a look at the following example and see why memory leaks happen. In the example below, object A refers to object B. A’s lifetime (t1 – t4) is much longer than B’s (t2 – t3). When B is no longer being used in the application, A still holds a reference to it. In this way, Garbage Collector can not remove B from memory. This would possibly cause out of memory problem, because if A does the same thing for more objects, then there would be a lot of objects that are uncollected and consume memory space.
It is also possible that B hold a bunch of references of other objects. Those objects referenced by B will not get collected either. All those unused objects will consume precious memory space.
3. How to Prevent Memory Leaks?
The following are some quick hands-on tips for preventing memory leaks.
- Pay attention to Collection classes, such as HashMap, ArrayList, etc., as they are common places to find memory leaks. When they are declared
static, their life time is the same as the life time of the application. - Pay attention to event listeners and callbacks. A memory leak may occur if a listener is registered but not unregistered when the class is not being used any longer.
- “If a class manages its own memory, the programer should be alert for memory leaks.”[1] Often times member variables of an object that point to other objects need to be null out.
4. A little Quiz: Why substring() method in JDK 6 can cause memory leaks?
To answer this question, you may want to read Substring() in JDK 6 and 7.
References:
[1] Bloch, Joshua. Effective java. Addison-Wesley Professional, 2008.
[2] IBM Developer Work. http://www.ibm.com/developerworks/library/j-leaks/
This article helps lot of information and useful.Explore more about SaaSCounter for all busness SaaS solution make your business easy.
Good Blog, Thanks!
home remedies and renowned culinary
Hotel hotel management system (HMS) works on an algorithm that helps to set prices for their rooms. The core purpose of the revenue management system is to provide optimum and competitive prices in the market. The hotel industry is a dynamic sector that frequently changes according to time and market trends; it is essential to have a hotel booking software .
The best hotel management software in India will understand the market trends and the business peak season. According to the seasonality, it adapts the prices when it is off-season it will reduce the room prices and increase it during the season time. That is why it is a beneficial tool that helps advanced planning and reduces unnecessary expenditures. It is an effective solution that not only helps to provide strategic pricing and make more revenue but also has additional benefit hotel front desk software
Thanks Patson it is useful post
I also refer very helpful and useful article about What are memory leaks in java
Please visit this article
http://www.mindstick.com/forum/33440/What%20are%20memory%20leaks%20in%20java#.Ve69Ppc0Xcc
http://www.javacodegeeks.com/2011/07/java-and-memory-leaks.html
Once you have the leak, these are the some quick options to fix them:
1) Get a HeapDump and analyze with a good tool such us IBM HEAP Analyzer
2) Use javosize, it is free and here you have how to do it: http://www.javosize.com/gettingStarted/topFatStaticVariables.html
3) Finally Plumbr is specialist in finding memory leaks, although not free: https://plumbr.eu
Yes, you are welcome to do that. Remember to give me a back link 😉
Can I translate it into Chinese and publich it in my blog? http://www.cnblogs.com/bylomo/
if A holds a reference to B , dose it mean that B is still being used ?
You should also be careful of singleton object that references large objects
so the way to prevent memory leakage is just to pay attention*3? i think you can put some more detailed things
good tutorial! thanks!
I don’t know what this article says..
poor my english
” Pay attention to event listeners and callbacks. A memory leak may occur if a listener is registered but not unregistered when the class is not being used any longer. ” in android developing i always do this ,but i do not very clear can you explain more deeper .
Considering the subject of this article being Java and Memory Leak at the same time, I’m a little disappointed that there isn’t any mention to WeakReference. Other than that, a very nice reading, thank you!